[2018-February-NEW] Step By Step Preparation for The Most Recommended Cisco 300-365 Dumps WIDEPLOY Exam Deploying Cisco Wireless Enterprise Networks Free Youtube Download Online (Update Questions) 36-54
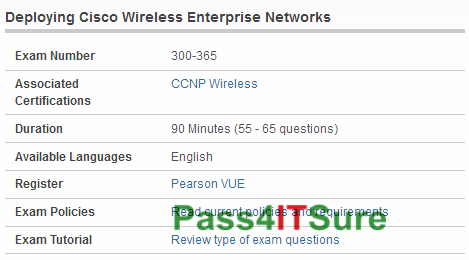
What are the best study tools for the Cisco 300-365 dumps? The Deploying Cisco Wireless Enterprise Networks (300-365 WIDEPLOY) exam is a 90 Minutes (55 – 65 questions) assessment in pass4itsure that is associated with the CCNP Wireless certification. Step by step preparation for the most recommended Cisco 300-365 dumps WIDEPLOY exam Deploying Cisco Wireless Enterprise Networks free Youtube download online.”Deploying Cisco Wireless Enterprise Networks” is the exam name of Pass4itsure Cisco 300-365 dumps test which designed to help candidates prepare for and pass the Cisco 300-365 exam. I will help you out by presenting one reliable source of Cisco https://www.pass4itsure.com/300-365.html dumps Deploying Cisco Wireless Enterprise Networks (WIDEPLOY) exam preparation.
[2018-February-NEW Cisco 300-365 Dumps From Google Drive]:https://drive.google.com/open?id=1G_BGbDqQ_nwjO5Wle0N-RndiD58yTtFS
[2018-February-NEW Cisco 352-001 Dump From Google Drive]: https://drive.google.com/open?id=1paDK-9hA4VkAHWxKstOh1F9h-pg93_fm
★Share some Citrix Specialist Pass4itsure 300-365 Dumps with Exam Questions and Answers Below(36-54)★
QUESTION 36
While implementing an approved change, a critical defect was introduced. Removing the defect will delay
the product delivery. What is the MOST appropriate approach to managing this situation?
A. Utilize the change control process.
B. Crash the schedule to fix the defect.
C. Leave the defect in and work around it.
D. Fast-track the remaining development.
300-365 exam Correct Answer: A
QUESTION 37
Which tool and technique identifies inefficient and ineffective policies, processes, and procedures?
A. Scope audits
B. Scope reviews
C. Quality audits
D. Control chart
Correct Answer: C
QUESTION 38
Which type of analysis would be used for the Plan Quality process?
A. Schedule
B. Checklist
C. Assumption
D. Cost-Benefit
300-365 dumps Correct Answer: D
QUESTION 39
The integrative nature of project management requires which Process Group to interact with the other
Process Groups?
A. Planning
B. Executing
C. Monitoring and Controlling
D. Project Management
Correct Answer: C
QUESTION 40
Which is a tool or technique used in Define Scope?
A. Templates, forms, and standards
B. Change requests
C. Product analysis
D. Project assumptions
300-365 pdf Correct Answer: C
QUESTION 41
Identifying major deliverables, deciding if adequate cost estimates can be developed, and identifying tangible components of each deliverable are all part of which of the following?
A. Work breakdown structure
B. Organizational breakdown structure
C. Resource breakdown structure
D. Bill of materials
Correct Answer: A
QUESTION 42
What is the function of a Project Management Office (PMO)?
A. To focus on the coordinated planning, prioritization, and execution of projects and subprojects that are tied to the parent organizations or the client’s overall business objectives.
B. To coordinate and manage the procurement of projects relevant to the parent organization’s business objectives and to administer the project charters accordingly.
C. To administer performance reviews for the project manager and the project team members and to handle any personnel and payroll issues.
D. To focus on the specified project objectives and to manage the scope, schedule, cost, and quality of the work packages.
300-365 vce Correct Answer: A
QUESTION 43
Which type of analysis systemically gathers and analyzes qualitative and quantitative information to determine which interests should be taken into account throughout the project?
A. Product
B. Cost-benefit
C. Stakeholder
D. Research
Correct Answer: C
QUESTION 44
Which of the following is an output of the Define Activities process?
A. Activity list
B. Project plan
C. Activity duration estimates
D. Project schedule
300-365 exam Correct Answer: A
QUESTION 45
When is a project finished?
A. After verbal acceptance of the customer or sponsor
B. After lessons learned have been documented in contract closure
C. When the project objectives have been met
D. After resources have been released
Correct Answer: C
QUESTION 46
Investment in security technology and processes should be based on:
A. clear alignment with the goals and objectives of the organization.
B. success cases that have been experienced in previous projects.
C. best business practices.
D. safeguards that are inherent in existing technology.
300-365 dumps Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
Organization maturity level for the protection of information is a clear alignment with goals and objectives of the organization. Experience in previous projects is dependent upon other business models which may not be applicable to the current model. Best business practices may not be applicable to the organization’s business needs. Safeguards inherent to existing technology are low cost but may not address all business needs and/or goals of the organization.
QUESTION 47
The data access requirements for an application should be determined by the:
A. legal department.
B. compliance officer.
C. information security manager.
D. business owner.
300-365 pdf Correct Answer: D
Explanation
Explanation/Reference:
Explanation:
Business owners are ultimately responsible for their applications. The legal department, compliance officer and information security manager all can advise, but do not have final responsibility.
QUESTION 48
From an information security perspective, information that no longer supports the main purpose of the business should be:
A. analyzed under the retention policy.
B. protected under the information classification policy.
C. analyzed under the backup policy.
D. protected under the business impact analysis (BIA).
Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
Option A is the type of analysis that will determine whether the organization is required to maintain the data for business, legal or regulatory reasons. Keeping data that are no longer required unnecessarily consumes resources, and, in the case of sensitive personal information, can increase the risk of data compromise. Options B. C and D are attributes that should be considered in the destruction and retention policy. A BIA could help determine that this information does not support the main objective of the business, but does not indicate the action to take.
QUESTION 49
The organization has decided to outsource the majority of the IT department with a vendor that is hosting servers in a foreign country. Of the following, which is the MOST critical security consideration?
A. Laws and regulations of the country of origin may not be enforceable in the foreign country.
B. A security breach notification might get delayed due to the time difference.
C. Additional network intrusion detection sensors should be installed, resulting in an additional cost.
D. The company could lose physical control over the server and be unable to monitor the physical security posture of the servers.
300-365 vce Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
A company is held to the local laws and regulations of the country in which the company resides, even if the company decides to place servers with a vendor that hosts the servers in a foreign country. A potential violation of local laws applicable to the company might not be recognized or rectified (i.e., prosecuted) due to the lack of knowledge of the local laws that are applicable and the inability to enforce the laws. Option B is not a problem. Time difference does not play a role in a 24/7 environment. Pagers, cellular phones, telephones, etc. are usually available to communicate notifications. Option C is a manageable problem that requires additional funding, but can be addressed. Option D is a problem that can be addressed. Most hosting providers have standardized the level of physical security that is in place. Regular physical audits or a SAS 70 report can address such concerns.
QUESTION 50
Effective IT governance is BEST ensured by:
A. utilizing a bottom-up approach.
B. management by the IT department.
C. referring the matter to the organization’s legal department.
D. utilizing a top-down approach.
Correct Answer: D
Explanation
Explanation/Reference:
Explanation:
Effective IT governance needs to be a top-down initiative, with the board and executive management setting clear policies, goals and objectives and providing for ongoing monitoring of the same. Focus on the regulatory issues and management priorities may not be reflected effectively by a bottom-up approach. IT governance affects the entire organization and is not a matter concerning only the management of IT. The legal department is part of the overall governance process, but cannot take full responsibility.
QUESTION 51
Which of the following is the BEST method or technique to ensure the effective implementation of an information security program?
A. Obtain the support of the board of directors.
B. Improve the content of the information security awareness program.
C. Improve the employees’ knowledge of security policies.
D. Implement logical access controls to the information systems.
300-365 exam Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
It is extremely difficult to implement an information security program without the aid and support of the board of directors. If they do not understand the importance of security to the achievement of the business objectives, other measures will not be sufficient. Options B and (‘ are measures proposed to ensure the efficiency of the information security program implementation, but are of less significance than obtaining the aid and support of the board of directors. Option D is a measure to secure the enterprise information, but by itself is not a measure to ensure the broader effectiveness of an information security program.
QUESTION 52
When an organization is implementing an information security governance program, its board of directors should be responsible for:
A. drafting information security policies.
B. reviewing training and awareness programs.
C. setting the strategic direction of the program.
D. auditing for compliance.
Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
A board of directors should establish the strategic direction of the program to ensure that it is in sync with the company’s vision and business goals. The board must incorporate the governance program into the overall corporate business strategy. Drafting information security policies is best fulfilled by someone such as a security manager with the expertise to bring balance, scope and focus to the policies. Reviewing training and awareness programs may best be handled by security management and training staff to ensure that the training is on point and follows best practices. Auditing for compliance is best left to the internal and external auditors to provide an objective review of the program and how it meets regulatory and statutory compliance.
QUESTION 53
A risk assessment and business impact analysis (BIA) have been completed for a major proposed purchase and new process for an organization. There is disagreement between the information security manager and the business department manager who will own the process regarding the results and the assigned risk. Which of the following would be the BES T approach of the information security manager?
A. Acceptance of the business manager’s decision on the risk to the corporation
B. Acceptance of the information security manager’s decision on the risk to the corporation
C. Review of the assessment with executive management for final input
D. A new risk assessment and BIA are needed to resolve the disagreement
300-365 dumps Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
Executive management must be supportive of the process and fully understand and agree with the results since risk management decisions can often have a large financial impact and require major changes. Risk management means different things to different people, depending upon their role in the organization, so the input of executive management is important to the process.
QUESTION 54
The FIRST step to create an internal culture that focuses on information security is to:
A. implement stronger controls.
B. conduct periodic awareness training.
C. actively monitor operations.
D. gain the endorsement of executive management.
Correct Answer: D
Explanation
Explanation/Reference:
Explanation:
Endorsement of executive management in the form of policies provides direction and awareness. The implementation of stronger controls may lead to circumvention. Awareness training is important, but must be based on policies. Actively monitoring operations will not affect culture at all levels.
See What Our Customers Are Saying
We at Pass4itsure are committed to our customer’s success. There are 50,000+ customers who used this preparation material for the preparation of various certification exams and this number of customers is enough for new candidates to trust in these products.Our Cisco 300-365 dumps are created with utmost care and professionalism. We utilize the experience and knowledge of a team of industry professionals from leading organizations all over the world.
The first thing you need to do is to understand the syllabus content and practice sufficient amount of Cisco 300-365 dumps sample questions. “Deploying Cisco Wireless Enterprise Networks”, also known as 300-365 exam, is a Cisco certification which covers all the knowledge points of the real Cisco exam. The next step is the selection of effective preparation material for CCNP Wireless Pass4iture 300-365 exam.Pass4itsure Cisco 300-365 dumps exam questions answers are updated (61 Q&As) are verified by experts. There are plenty of websites that provide https://www.pass4itsure.com/300-365.html dumps preparation material but you have to get your hands on the right one. The associated certifications of 300-365 dumps is CCNP Wireless.
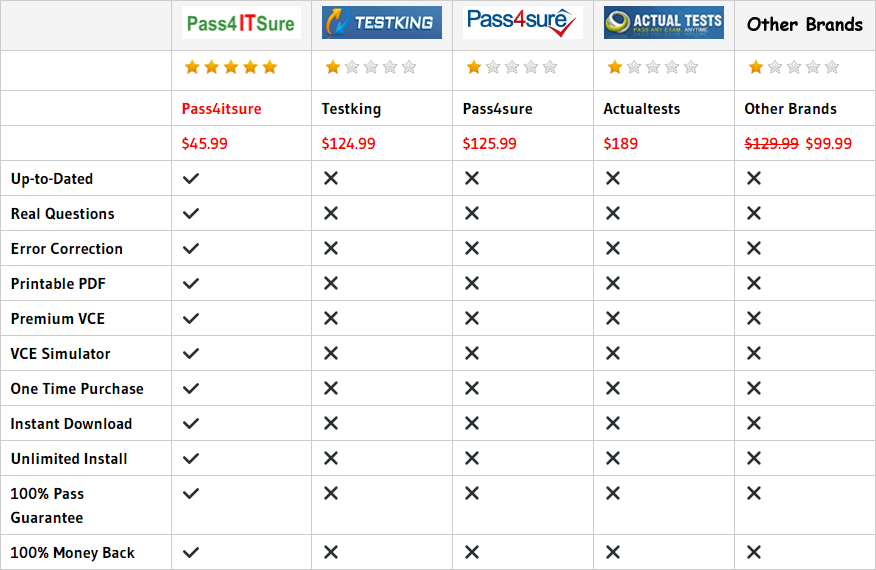
Compared with other brands, Pass4itsure has up to dated exam information, affordable price, instant exam PDF files downloaded, error correction, unlimited install,etc. Such as Pass4itsure Cisco 300-365 Dumps, The Most Recommended Cisco 300-365 Dumps Demo Download Online, We Help You Pass Deploying Cisco Wireless Enterprise Networks. Simple and Easy! To take advantage of the guarantee, simply contact Customer Support, requesting the exam you would like to claim. Pass4itsure guarantee insures your success otherwise get your MONEYBACK!
